How to contact me securely
Updated 6/7/24
Ordinary email gets to me fastest. Use my regular Contacts if you can. This page offers more secure and private alternatives.
Before you reach out, give some thought to what you want to keep private, who might try to listen in, and how much you care. The Electronic Frontier Foundation’s Surveillance Self Defense guide is a great resource.
SIGNAL
For most circumstances, the best and easiest choice is to install the Signal app and message me at 510-993-0820. Turn on the setting for Disappearing Messages. I do not use this number for voice calls or voicemail.
SEND ME A FILE
You can upload a file for me confidentially at https://bgell.me/sendfile. This takes you to a secure, end-to-end encrypted page hosted by Tresorit. No one but me can see the file, but you may leave digital traces of your identity. For strongest security and anonymity, see SecureDrop below.
THE OLD FASHIONED WAY
Postal mail can be a good choice for confidential material. The government scans the outside of every envelope, but a warrant is required to open and read what’s inside. You can use a boring, fake return address, or leave it blank. Address it to me at the Brennan Center, 120 Broadway, 17th floor, .
For an extra layer of protection, you can snail mail me the link to an encrypted message on pastebin.com or the server of your choice.
PGP ENCRYPTION
I have reduced my use of PGP. Signal (above) is usually a better choice. But if you prefer to use PGP my key is available here and on other key servers.
Make sure the key matches this fingerprint:
5FFB 9661 E80B EEAC F60A F439 9402 6C02 F396 3B70
Do not use any other key for me. Some have expired, and some may be imposters.
SECUREDROP
If you have genuine reason to fear surveillance by a well-resourced adversary, you may reach me on SecureDrop, a system designed for maximum privacy. It requires time and attention on your part, but no expertise. Fair warning: I do not check my SecureDrop often. This is not a good way to reach me quickly.
SecureDrop combines anonymity and encryption. No one, including me, will know who you are or where you are located. (SecureDrop can’t see your IP address.) No one but me is capable of reading the information you send.
To protect your anonymity, I recommend that you close this page now and clear your browser history. Then, using a computer that does not belong to your employer, go to a library or coffee shop with public wifi and come back to this page. Once you have done that, continue with “How to use SecureDrop,” below.
How to use SecureDrop
- You need the Tor Browser, which anonymizes you on the web, to reach my SecureDrop site. Download it here.
- Launch the Tor Browser on your computer and browse to one of the following two pages. Again, you can’t reach these pages with Chrome, Firefox, Edge, Safari or any other ordinary browser. Copy and paste either of these addresses into the Tor Browser:
- http://bartongellman.securedrop.tor.onion/ or
- http://hxywmnvdz5f2l5gqwjfcejdpla7nhj35dn5cf5l6qevjb77wasnna3qd.onion/
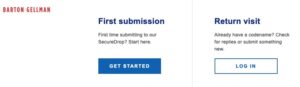
You will come to a page that looks like this. Click on Get Started and follow instructions from there.
 SecureDrop limitations and cautions
SecureDrop limitations and cautions
SecureDrop uses well-respected, open source tools for anonymity (Tor) and encryption (GPG, also known as OpenPGP). Outside experts have audited and improved the technology, but no system offers perfect security. For example, if someone installs spyware or a hardware key-logger on your computer, your communications with me may be compromised.
When you visit my SecureDrop page, I cannot see your computer’s I.P. address. I will not record information about your browser, computer, or operating system, nor will I embed third-party content or deliver cookies to your browser.
If you send me messages or files, I will make no attempt to identify you without your consent.
My SecureDrop servers are kept under lock and key in an undisclosed location, segregated from other computers and networks. I host the system on a Tor “hidden service,” which conceals your location and online identity as well as mine. SecureDrop encrypts all communications from your computer to mine.
All that said, the system is provided on an “as is” basis. I can make no warranty about its security, or yours, and in the end you must assess the risks for yourself.
